This issue was a bit of a brain cracker but I’m happy with the outcomes.
A few weeks ago, one of my freelance customers from Argentina called saying they noticed their users could connect to their corporate email infrastructure using unmanaged email clients, which, in traditional French is what they call a big information security ka-ka, that could potentially lead to data leaks or even worse.
To tell you a bit about the infra:
- It is a WS1 UEM On-Prem deployment
- The email server is Exchange on-prem and the customer is using WS1 SEG for email integration
- It’s a BYOD deployment having iOS and Android.
- All users should be using a hardened deployment of Boxer to connect to the environment
Upon checking we found out there were no email compliance policies set up, so if users tried to connect to the SEG and it had a proper set of credentials they would’ve been authenticated and able to sync email.
Please note: the settings described below will only apply for a BYOD approach where you are using WS1 boxer, if you want to allow your users to use native mail clients for corporate-owned devices this might not be the right solution for you.
How to solve this situation:
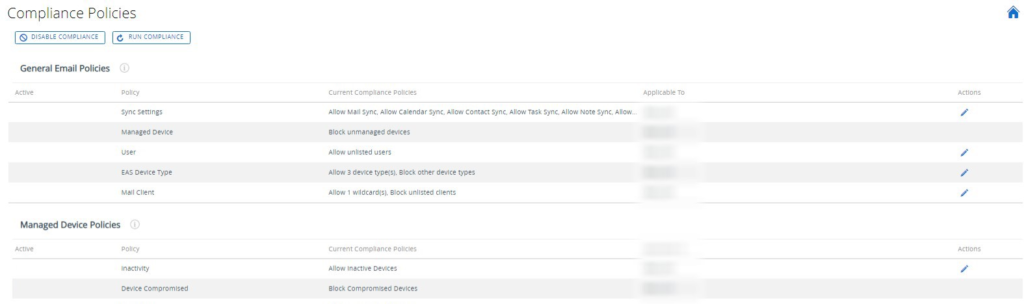
In Workspace One UEM console we browse to Email -> Compliance policies and we should see something like this:
Under EAS (Exchange Active Sync) Device Type we should configure the compliance policy like this:
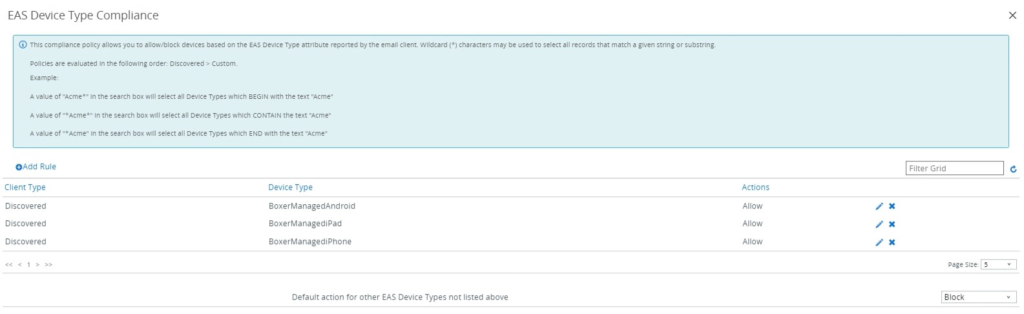
This setting will allow only Boxer clients and block all unmanaged clients.
Mail Client
Your mail client should look like this:
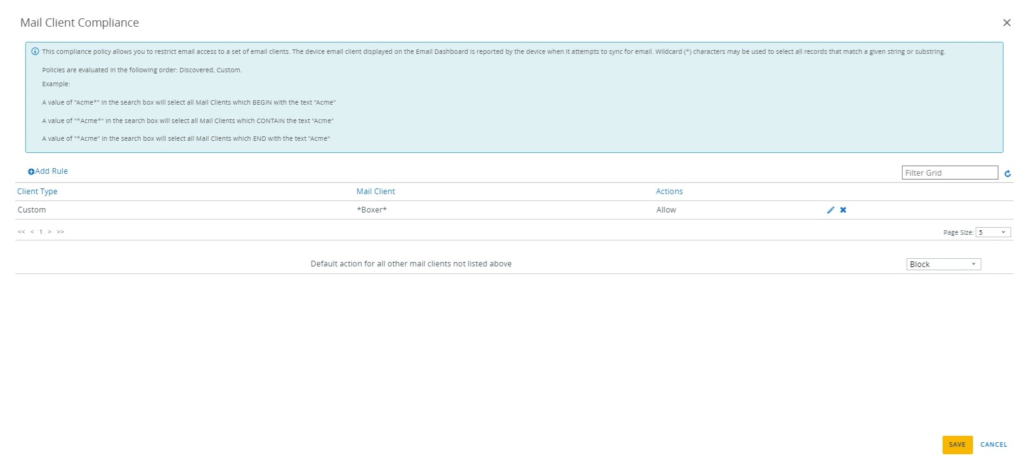
This way we will allow only boxer clients and block all other unmanaged clients.
Under Sync Settings compliance:
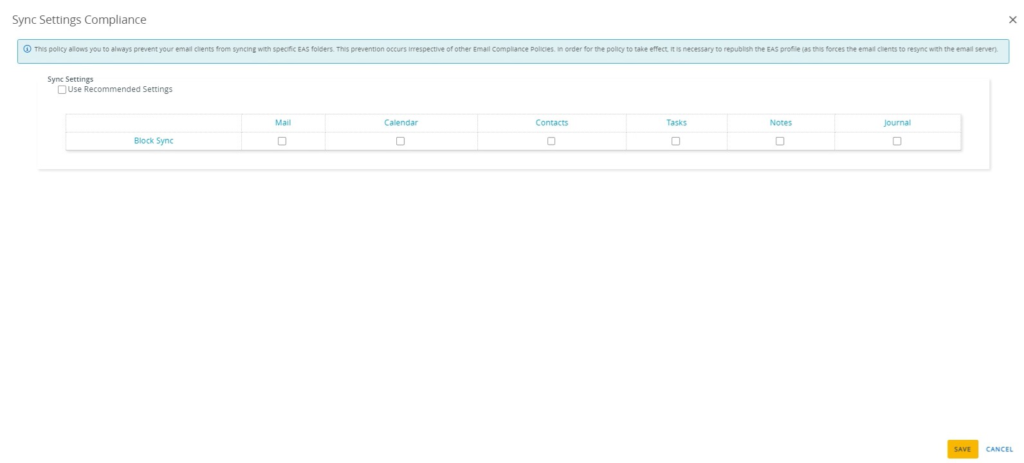
This setting will remove the email, calendar, contacts and other email objects sync from non-compliant devices.
Other settings to enable:
Device Compromised: Set to Block Compromised Devices
Managed Devices: Set to Block Unmanaged Devices
For an additional layer of security, the exchange team has decided to block unmanaged email clients on Exchange.
Here are the steps:
1. Log in to Exchange Console
2. Click Mobile -> Mobile Device Access
3. Under Exchange Active Sync Device Access Rules create 4 rules:
- One rule to allow BoxerManagedAndroid
- One rule to allow BoxerManagediPhone
- One rule to allow BoxerManagediPad
- One rule to block the remaining devices.
I got the idea from this video from Ben Siler
https://www.youtube.com/watch?v=jQ1KtUpOZGI
